Aadhaar scores 0/10 on mobile app security, says grey hat hacker in middle of flame war with UIDAI
Sriram Sharma January 17, 2018 8 min

The security of UIDAI’s Aadhaar project has come under intense scrutiny from international researchers of late, and in the eye of the storm is Baptiste Robert, a mysterious French researcher who goes by the name of Elliot Alderson on Twitter. Named after the protagonist of the TV series Mr. Robot, his handle is an l337speak spin on the fictional hacktivist group fsociety from the series. Alderson, who has spent the last week researching and disclosing vulnerabilities in the mAadhaar app, and UIDAI’s mobile security practices on the whole, has elicited dread, facepalms, and mirth from the infosec community at large.
“I guess this app had been made by interns or junior developers,” says Alderson, rating UIDAI’s mobile app security as 0/10 in an emailed interview with FactorDaily. (He declined our requests to do a face-to-face video call, or a telephonic interview.) More on his Aadhaar-related findings later. Who is Baptiste Robert? Is he a real person, and what motivates him?
Here’s what we’ve found: it’s quite likely that he is a French citizen, considering his prior interviews, particularly this one by a French newspaper. In another interview, he says he’s 28 year old. His Twitter handle has been active since 24th October 2017, and his first tweet was aimed at the French CNRS (Center for Scientific Research). In less than a hundred days, he has gained over 15,000 followers thanks to his unconventional style, which relies heavily on Twitter feedback, and flies in the face of responsible disclosure.
“I’m not a fanboy of Mr Robot, I just think it is fun to create this character on Twitter,” he says, describing himself as a freelance developer. “I’m working as an Android developer and AOSP (Android Open Source Project) expert for European companies,” he says. As for his obsession with privacy, he feels that it’s a big subject which deserves more coverage from around the world, but doesn’t get enough attention due its technical nature. He claims to be sole member of fsociety at this point. We weren’t able to find any online profiles linking to his name or identity online.
White Hat or Black Hat?
“I’m not a black hat. I don’t earn money with my findings and don’t exploit it in malicious ways,” says Alderson. “I’m not really a white hat too, because I don’t follow the standard responsible disclosure standards. I’m more of a grey hat,” he says. A grey hat hacker is a bit of both shades — someone with the skills and intent of a white hat hacker, but also someone who will infiltrate or explore a system or network without permission or clearance. There’s a thread where he’s archived his recent research of app and phone makers, including Facebook, CM Browser, OnePlus, Xiaomi, Paypal, Wiko Mobile, Archos, and MakeMyTrip, among others.
View image on Twitter
 Elliot Alderson@fs0c131y
Elliot Alderson@fs0c131y
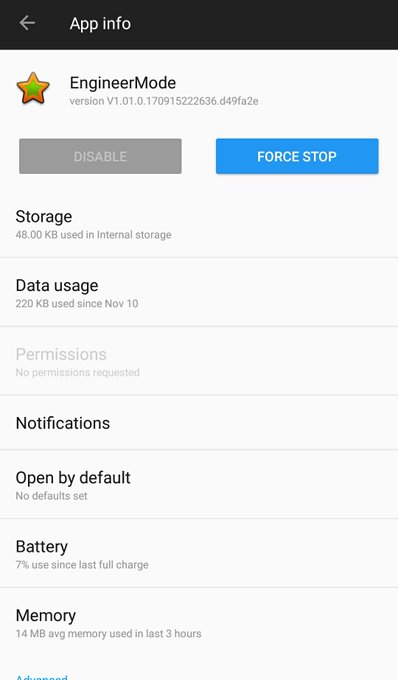
This app is a system app made by @Qualcomm and customised by @OnePlus. It's used by the operator in the factory to test the devices.
3:48 AM - Nov 14, 2017
7070 Replies
754754 Retweets
904904 likes
Twitter Ads info and privacy
“It’s not ethical to reveal vulnerabilities, live on Twitter. But for the kind of security statements we’ve been getting from the government we need guys like him”, says an Indian security researcher who didn’t want to be named. A lot of voices on Twitter have also appreciated his work.
Digging into mAadhaar
Alderson, who has an open DM setting on Twitter seems to have been tipped off by someone to take a look into UIDAI’s apps sometime last week. It doesn’t seem like there’s anything political or ideological motivation against national biometric IDs driving his investigation. “At first, I didn’t know what Aadhaar is. It seems to be something with strong cultural and political ramifications. I’m clearly not legitimate to give an advice on it. I’m limiting myself to the security of the Android app.” he says.
In case you haven’t been following his exploits, here’s a quick recap of UIDAI’s security issues found by him in the mAadhaar app, which allows users to carry a digital copy of their Aadhaar card on the smartphone. At the time of filing our previous feature, he had decompiled the app and extracted the database password and password salt, and concluded that everyone has the same password set on their app.
View image on Twitter

 Elliot Alderson@fs0c131y
Elliot Alderson@fs0c131yHi #Indian people! #Hackers are already at work. Afaik, I found the 1st #Aadhaar malware (a modified version of the official #Aadhaar #android app) on the web: https://www.virustotal.com/#/file/d1170fa637def71e9fd50fbaf1a6c180edaa07859c09d67654302587ab1e9689/detection …
VT score: 2/62
cc @malwrhunterteam @virqdroid @LukasStefanko @JAMESWT_MHT
10:55 AM - Jan 13, 2018
2828 Replies
542542 Retweets
432432 likes
Twitter Ads info and privacy
Among his other findings, he’s uncovered the first instance of Aadhaar malware, mAadhaar’s app certificate permission set to defaults, which leads him to believe that UIDAI has lost access the primary key to update the app on Google Play. Considering the mAadhaar app hasn’t been updated since the week it was launched (22nd July 2017), this may be a troublesome prospect for UIDAI, which will leave existing users vulnerable, even if they delist the app from the Play Store altogether.
 Two new apps appeared on UIDAI’s account on Google Play on Sunday, and Alderson was quick to point this out and pounce on the opportunity to investigate further.
Two new apps appeared on UIDAI’s account on Google Play on Sunday, and Alderson was quick to point this out and pounce on the opportunity to investigate further.On Sunday, he also found a couple of test apps hosted by UIDAI’s Google Play account, leading to the profile of a developer called Wferr who upon being confronted on Twitter denied that he had anything to do with it. It’s a mystery to everyone, including Alderson. Could it be that his code was copy-pasted from somewhere else, leading to his mail being published with the app? “I discussed with him (Wferr) by DM. This is weird and I don’t have a rational explanation here,” Alderson says.
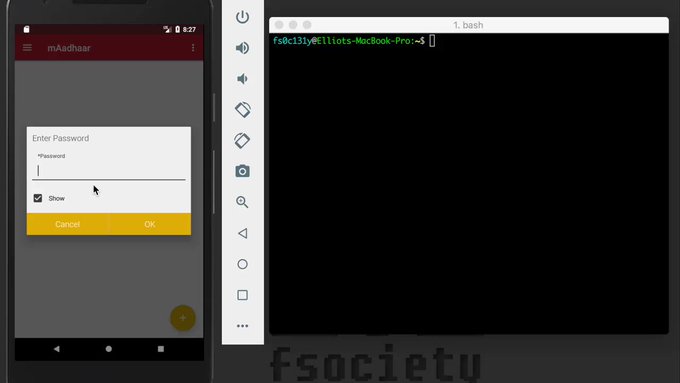
Alderson posted a video on Monday demonstrating how an attacker can bypass the password protection of the app, and access a user’s Aadhaar information. On Tuesday, he posted another video showing the password protection being bypassed. So what’s new in his latest exploit? “This one does not need a rooted phone. It works on every device. The attacker just have one command to send, and will be able to change the password and access the Aadhaar info. He does not necessarily need a computer, he can use an app like Termux for example, to send the command.” he explains.
 Elliot Alderson@fs0c131y
Elliot Alderson@fs0c131yHi my #Indian friends
 ! Let me show you another way to bypass the password protection in the official #Aadhaar #Android app.
! Let me show you another way to bypass the password protection in the official #Aadhaar #Android app.Once again, in less than 1 minute, an attacker can access your #Aadhaar informations without having your password #AadhaarFail
7:39 PM - Jan 16, 2018
5353 Replies
617617 Retweets
618618 likes
Twitter Ads info and privacy
“Do they really have a security team?,” he says, when we asked if he had any advice or feedback for UIDAI’s security team, and if these issues can be fixed. “They have to hire experienced developers. Of course, things can be fixed,” he says. “For a project with this importance, they have to take the security of the data they handle seriously.”
Data Brokers Beware
There are other data privacy concerns that a smartphone user now needs to worry about,such as data brokers. Considering the number of paranoid users who have mentioned it, we were curious to know if he had come across of any instances of apps created by adtech or marketing tech companies that were eavesdropping on users. “Eavesdropping, not yet. I found eye-tracking once,” Alderson says.
We also wanted to hear his opinion on whether Android a particularly insecure operating system, considering a lot of his work is focused on it. “Android is an awesome OS and each dessert (version of Android) is better in term of security,” he says, with a couple of caveats. “The reality is that it’s clearly super easy for a script kiddie to make an Android malware. Moreover, Google really has to clean the Play Store,” he says.
As for the tools of his trade, while he doesn’t have any strong recommendations for any particular tool, he says jadx (a tool to decompile Android apk files into Java source code), Apktool (a tool for reverse engineering Android apk files), and Baksmali (an assembler/disassembler for the dex format) are some famous tools among security researchers.
We were also curious to know which phone manufacturer, in his opinion is the worst violator of user privacy. “I don’t like giving names but the cheaper the phone is, the worse it is in term of privacy,” he says. As for which phone he uses, we know that he uses a OnePlus 5T, despite his research on backdoors found on it. “Actually, OnePlus 5T is a pretty good phone. I have a lot of phones,” he says.
“My goal is to denounce publicly the abuses made by these companies,” he says, explaining the overarching thesis behind his work. As for why he thinks data privacy is an important issue for citizens around the world, he believes it’s just good common sense. “Are you ready to give your personal info, address, age, gender, sexuality, your personal photos to a stranger on the street? I’ll bet no. It’s the same thing with an app. They collect your data, sell it to third parties, exploit it,” he says.
